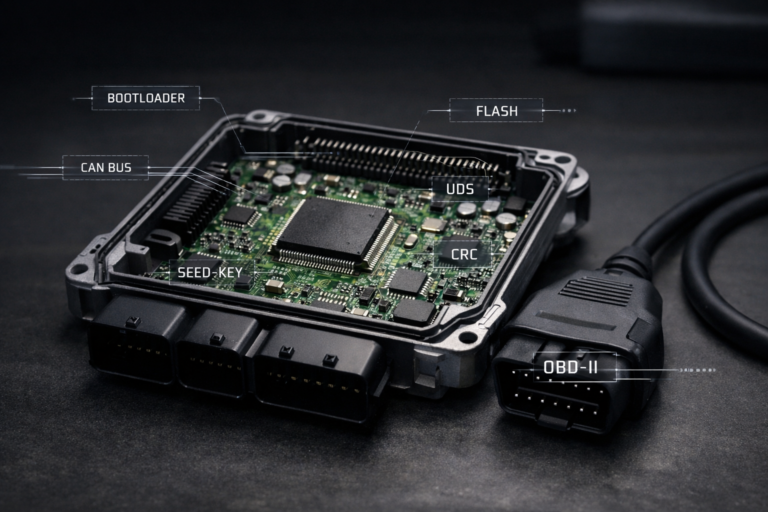
Modern vehicle security has evolved dramatically over the past two decades — but so have the methods thieves use to bypass it. One of the most alarming trends in recent years is CAN Injection, a technique that doesn’t clone your key or jam your signal — it talks directly to your car’s brain.
Below, we’ll break down how this attack works, why it’s so effective against today’s high-end ECUs, and the underlying math that makes it possible — and how tuners and security experts alike can better understand the weak spots.
What Exactly is CAN Injection?
A modern vehicle’s ECUs communicate through a Controller Area Network (CAN bus). This is a two-wire differential bus — every module (immobilizer, BCM, camera, door locks, powertrain, etc.) listens and broadcasts messages using an arbitration-based priority scheme.
In a keyless entry scenario, the legitimate workflow is:
-
Fob broadcasts an encrypted signal.
-
BCM authenticates it.
-
ECU/immobilizer verifies the rolling code.
-
If valid, the CAN bus carries an “Unlock + Start” command.
CAN Injection bypasses the fob entirely. Instead, a rogue device connects to exposed wiring (e.g., headlamp harness) and transmits forged frames that mimic an authorized “Unlock + Start” handshake.
The CAN Protocol: Arbitration & Bitwise Dominance
At its core, the CAN bus uses a bitwise arbitration mechanism based on the concept of dominant (logical 0) and recessive (logical 1) states:
-
If multiple nodes transmit simultaneously, the one sending dominant bits overrides recessive bits on the bus.
-
Each message starts with an 11-bit or 29-bit ID field. Lower binary IDs have higher priority because a ‘0’ beats a ‘1’ in arbitration.
Mathematically:
-
Bus State:
S(t) ∈ {0,1} -
If Node A transmits
0110and Node B transmits0101, then:-
Bit 1: both send 0 → bus = 0
-
Bit 2: both send 1 → bus = 1
-
Bit 3: A sends 1, B sends 0 → bus = 0 (B wins)
-
Node A detects mismatch, stops transmitting.
-
This allows multiple ECUs to share the same wires without collisions — but also means that a rogue node can dominate the bus with carefully crafted IDs and bit timings.
Dominant Override Attacks
Some real-world CAN Injection devices employ dominant override: they drive the bus to maintain a constant dominant (0) state for specific bits, preventing legitimate ECUs from transmitting recessive bits needed for valid traffic.
Think of it like this:
-
Legit ECU needs to send
1010. -
Attacker injects dominant ‘0’s where it expects a ‘1’.
-
The bus resolves to
1000. -
Legit ECU detects bit mismatch, drops frame.
-
Attacker’s forged frame sails through.
Message Timing: A Tiny Window
Timing is critical:
A CAN frame’s bit time Tbit is:
For a 500 kbps CAN bus, Tbit = 2 µs. So, each bit has just 2 microseconds to settle and propagate. An injection device must:
-
Synchronize with the bus clock.
-
Inject dominant bits at the exact moment.
-
Avoid generating bus errors that trigger failsafe modes.
This is why attackers use microcontrollers with precise CAN transceivers (e.g., PIC18F series with built-in ECAN modules).
Real-World Example: RAV4 Theft
In documented cases, attackers:
-
Physically access the headlamp wiring — easily reachable from outside.
-
Connect a disguised device that pulls power from the light circuit.
-
Send a forged message that says, “Key verified.”
-
Immobilizer unlocks; car starts.
The math behind this:
-
The attacker must replicate the exact CAN ID, DLC (Data Length Code), and data payload.
-
For rolling codes or session keys, they replay a valid captured frame or brute-force a static response if weaknesses exist.
Defending Against CAN Injection
Protocol-level defense: Add cryptographic signatures to frames. Mathematically:
On receive:
Gateway filtering: Add hardware that detects suspicious bit timing:
But note: sophisticated attacks can throttle messages to stay below thresholds.
Physical design: Harden easy access points (e.g., avoid exposed harnesses).
Final Thoughts for Tuners
For the tuning world, understanding the CAN bus deeply is not just about adding power — it’s about respecting how fragile in-vehicle networks really are. Any improper flash or poorly implemented module can open the same door a thief does — unintentionally.
At Eagle tuning, we see this not just as a security risk but as a reminder that every read/write on the CAN bus needs clean math, solid timing, and respect for the original design.